Blockchain is an append-only electronic distributed ledger database technology. The protocol ensures that each block of data is tamper proof, secure, decentralized, verified and fingerprinted (or hashed) before it is appended to the chain.
For example: Currently, most enterprise companies like Facebook, Amazon and Microsoft run a data monopoly, meaning that all user data that are collected are stored in a central database controlled by the entity. The user has little to no control on how that data is used, shared, stored, updated, etc.
Blockchain is an append-only electronic distributed ledger database. While the term “Blockchain” is relatively new, the underlying technologies have been in existence for 20+ years. Blockchain relies on the following existing technologies–
Features
At a very high level, blockchain relies on the following existing technologies–
-
Cryptography – The fact that each blockchain record contains a unique cryptographic hash that is used to track that block, as well as others in the associated chain, means data cannot be modified (immutable). That makes it perfect for record keeping and auditing purposes.
-
Distributed Ledger Technology (DLT) – What makes a blockchain a special kind of ledger is that instead of being managed by a single centralized institution, such as a bank or government agency; rather, copes of the data are stored on multiple independent computers within a decentralized network. No single entity controls the ledger. Any of the computers on the network can make a change to the ledger, but only by following rules dictated by a “consensus protocol. Any changes made to the ledger are then broadcasted to all the nodes on the network. Then all nodes are updated to reflect those changes.
-
Consensus Algorithm – a mathematical algorithm that requires a majority of the other computers on the network to agree with the change. Consensus protocol comes in 2 flavors –
-
Permissioned and Permissionless
Within this general framework are many variations. There are different kinds of consensus protocols, for example, and often disagreements over which kind is most secure. There are public, “permissionless” blockchain ledgers, to which in principle anyone can hitch a computer and become part of the network; these are what Bitcoin and most other cryptocurrencies belong to. There are also private, “permissioned” ledger systems that incorporate no digital currency. These might be used by a group of organizations that need a common record-keeping system but are independent of one another and perhaps don’t entirely trust one another—a manufacturer and its suppliers, for example.
-
-
Once a consensus generated by that algorithm has been achieved, all the computers on the network update their copies of the ledger simultaneously. If any of them tries to add an entry to the ledger without this consensus, or to change an entry retroactively, the rest of the network automatically rejects the entry as invalid.
- Immutability – As mentioned above, data recorded on each block, once verified and accepted via consensus by all the nodes, cannot be modified or deleted. Any attempt to modify or delete a data on a block will render that block as well as the prior block non-compliant and therefore unacceptable.
- Smart Contracts – are programmed instructions that are automatically executed when certain conditions are met. Smart contracts are similar to IF THEN ELSE statements embedded in contracts. Ex- do something (e.g., release code) if something else is true (test of code is completed and approved). Example, an attorney might create a smart contract “will” that is stored on a blockchain. In that case, in the event of an event, then the will is executed automatically, precisely as the owner stipulated without any human intervention or misunderstanding of the intent of the owner.
-
Trustless – Historically, society has relied on centralized authorities to establish trust between unknown parties in order to facilitate transactions and to execute contracts. These central authorities have served as custodians of trust for the millennia. Just imagine doing any business today without third party intermediaries. This is about to change thanks to blockchain. Because it is decentralized, transparent to all stakeholders and immutable, blockchain has trust built into its operations so it does not rely on a third party with a siloed and centralized database which are often subject to tempering and hacking.
-
Hashing – Takes the input on a given block in addition to the hash of the prior block and runs it through SHA-256 hashing algorithm and produces a new hash function that is then used to secure its place in the chain of blocks. This is one of the secure features of blockchain that makes it immutable and difficult to hack. If the content on a block is altered, then that block will be rejected by the blocks prior and after that block. So the only way to compromise a block is to solve a complex mathematical problem that alters the particular block and all other blocks before it along with all the decentralized block in the network. All these has to be done in a specific time limit for it to be accepted.
How the hashing process works using the SHA-256 hash calculator
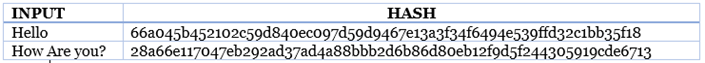
Fig 2.
Part 1: Difference between Blockchain and Bitcoin — Part 3: Why Blockchain is the next platform for Applications
